Configuration of Microsoft ISA Proxy Server and Linux Squid Proxy Server E-Book
Dr. Hidaia Mahmood Alassouli
Erhalten Sie Zugang zu diesem und mehr als 300000 Büchern ab EUR 5,99 monatlich.
- Herausgeber: Dr. Hidaia Mahmood Alassouli
- Kategorie: Wissenschaft und neue Technologien
- Sprache: Englisch
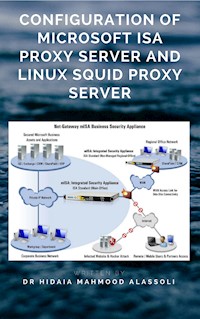
The paper concerns about basic Microsoft ISA server and Linux Squid Server configuration As a lot of technicians switch between ISA server and Squid server, I decided to write this paper to present some reference when configuring ISA and Squid. There a lot of issues that not covered, and you can go to the manual of ISA server and Squid server for detailed configuration of ISA and Squid. The paper is composed from two parts 1.Microsoft ISA server 2004 Configuration2.Linux Squid Server ConfigurationNote that, this work was done without proper simulation, because of the lack of resources, as testing firewall configuration requires many computers, with one of them should have many network cards. Also the ISA server is not used in the computer center now.
Sie lesen das E-Book in den Legimi-Apps auf:
Seitenzahl: 35
Veröffentlichungsjahr: 2020
Das E-Book (TTS) können Sie hören im Abo „Legimi Premium” in Legimi-Apps auf:
Ähnliche
Configuration of Microsoft ISA Proxy Server and Linux Squid Proxy Server
By
Dr. Hidaia Mahmood Alassouli
1. OVERVIEW
The paper concerns about basic Microsoft ISA server and Linux Squid Server configuration As a lot of technicians switch between ISA server and Squid server, I decided to write this paper to present some reference when configuring ISA and Squid. There a lot of issues that not covered, and you can go to the manual of ISA server and Squid server for detailed configuration of ISA and Squid. The paper is composed from two parts
Microsoft ISA server 2004 Configuration
Linux Squid Server Configuration
Note that, this work was done without proper simulation, because of the lack of resources, as testing firewall configuration requires many computers, with one of them should have many network cards. Also the ISA server is not used in the computer center now.
KEYWORDS:
Internet Security Acceleration Server, ISA Server, Squid Server, Proxy, Firewall.
2. MICROSOFT ISA SERVER 2004
2.1 MAIN OPERATION:
All of the network rules and access rules make up the firewall policy. The firewall policy is applied in the following way:
1. A user using a client computer sends a request for a resource located on the Internet.
2. If the request comes from a Firewall Client computer, the user is transparently authenticated using Kerberos or NTLM if domain authentication is configured. If the user cannot be transparently authenticated, ISA Server requests the user credentials. If the user request comes from a Web proxy client, and the access rule requires authentication, ISA Server requests the user credentials. If the user request comes from a SecureNAT client, the user is not authenticated, but all other network and access rules are still applied.
3. ISA Server checks the network rules to verify that the two networks are connected. If no network relationship is defined between the two networks,
the request is refused.
4. If the network rules define a connection between the source and destination networks, ISA Server processes the access rules. The rules are applied in order of priority as listed in the ISA Server Management interface. If an allow rule allows the request, then the request is forwarded without checking any additional access rules. If no access rule allows the request, the final default access rule is applied, which denies all access.
5. If the request is allowed by an access rule, ISA Server checks the network rules again to determine how the networks are connected. ISA Server checks the Web chaining rules (if a Web proxy client requested the object) or the firewall chaining configuration (if a SecureNAT or Firewall Client requested the object) to determine how the request will be serviced.
6. The request is forwarded to the Internet Web server.
2.2 TYPE OF NETWORKS AND NETWORK RELATIONSHIPS AND ISA SERVER CLIENTS:
The default type of networks,
VPN Clients-
Built-in dynamic network object representing client computers connected to ISA Server via VPN.
Internal-
Network representing the internal network, i.e. 10.12.00.00 -10.12.255.254.
Local Host-
Built-in network object representing the ISA Server computer
Quarantined VPN Clients-
Built-in dynamic network representing client computers connecting to ISA Server via VPN that are currently quarantined.
Perimeter-
Network object representing a perimeter network (also known as DMZ, demilitarized zone, and screened subnet).
External-
Network object representing the Internet.
There are two types of network relationships:
ISA Server provides secure access to internet for all of its clients. ISA server has three type of clients:
Firewall clients: